Industrial IoT Certification: What Matters Before System Rollout
Before any connected factory system goes live, Industrial IoT certification can determine whether deployment delivers resilience or exposes hidden compliance, safety, and data-integrity risks. For quality control and safety managers, understanding what truly matters before rollout is essential to protecting uptime, ensuring traceability, and aligning industrial infrastructure with globally recognized performance and reliability standards.
Why a checklist-first approach works better before Industrial IoT rollout
For quality and safety teams, Industrial IoT certification is rarely just a document review. It is a decision gate that affects equipment release, plant safety, supplier accountability, and long-term data trust. A checklist-first approach helps teams avoid the most common rollout mistake: approving a connected system based on functionality alone while leaving compliance, cybersecurity, environmental endurance, or calibration traceability unresolved.
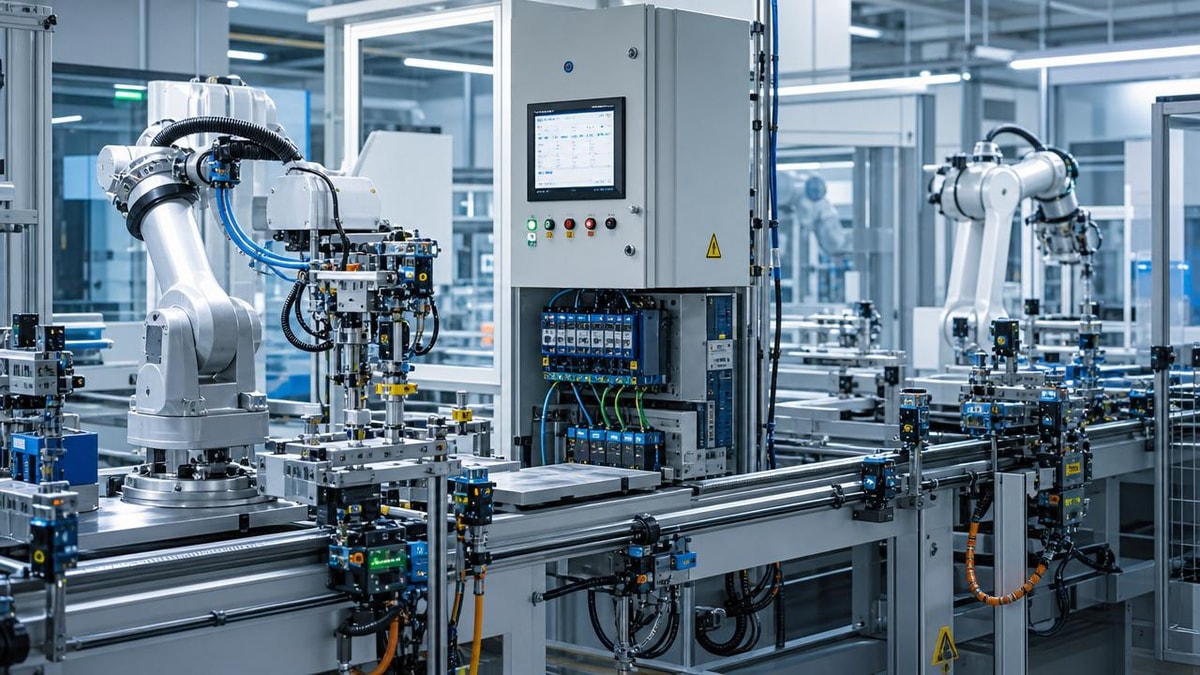
This matters even more in complex industrial environments where semiconductor handling, power electronics, sensors, packaging lines, clean environments, and process utilities interact. In these settings, a device can pass a demo and still fail in production because it was not certified for the actual risk profile of the site. Industrial IoT certification should therefore be reviewed as an operational readiness filter, not as a procurement afterthought.
The practical question is simple: before system rollout, what must be checked first, what can be validated next, and what should never be assumed? The following guide is organized to answer exactly that.
The first-pass Industrial IoT certification checklist
Before reviewing vendor claims in detail, quality control and safety managers should confirm whether the certification scope matches the real deployment environment. The following checklist is the fastest way to identify gaps early.
- Confirm whether the certified product version is the same hardware, firmware, and communication module planned for rollout. Small model differences can invalidate a certificate’s relevance.
- Check whether the certification applies to the intended installation environment, including temperature range, humidity, vibration, electromagnetic exposure, ingress protection, and hazardous area requirements.
- Verify whether safety, EMC, wireless, cybersecurity, and data integrity requirements were assessed separately or as part of a complete conformity package.
- Review whether calibration, measurement accuracy, drift tolerance, and sensor repeatability are covered by recognized testing methods.
- Ask whether testing was performed by accredited laboratories, ideally under ISO/IEC 17025 or an equivalent recognized framework.
- Determine whether the supplier can provide change control records for firmware updates, component substitutions, and manufacturing process revisions.
- Ensure the documentation includes maintenance limits, recertification triggers, and conditions that would void compliance.
If any one of these items is unclear, Industrial IoT certification should be treated as incomplete for rollout approval purposes.
What to verify in the certification scope before approving deployment
1. Product identity and version control
The most overlooked issue in Industrial IoT certification is version mismatch. A certificate may refer to a platform family, while the plant receives a modified unit with different firmware, radio modules, power stages, or sensor elements. Quality managers should request the exact part number, revision history, bill of materials status, and firmware release record. Safety managers should also ask whether any field configuration can change the certified operating envelope.
2. Electrical safety and EMC fitness
In connected industrial systems, electrical safety and electromagnetic compatibility are foundational. A certified sensor gateway or edge controller that suffers from conducted noise, transient susceptibility, or grounding instability may create false alarms, bad data, or unsafe equipment states. Review test evidence for surge immunity, electrostatic discharge, radiated emissions, power supply tolerance, and grounding recommendations. In power-dense environments such as motor drives, converters, and semiconductor tools, this is especially important.
3. Environmental and mechanical suitability
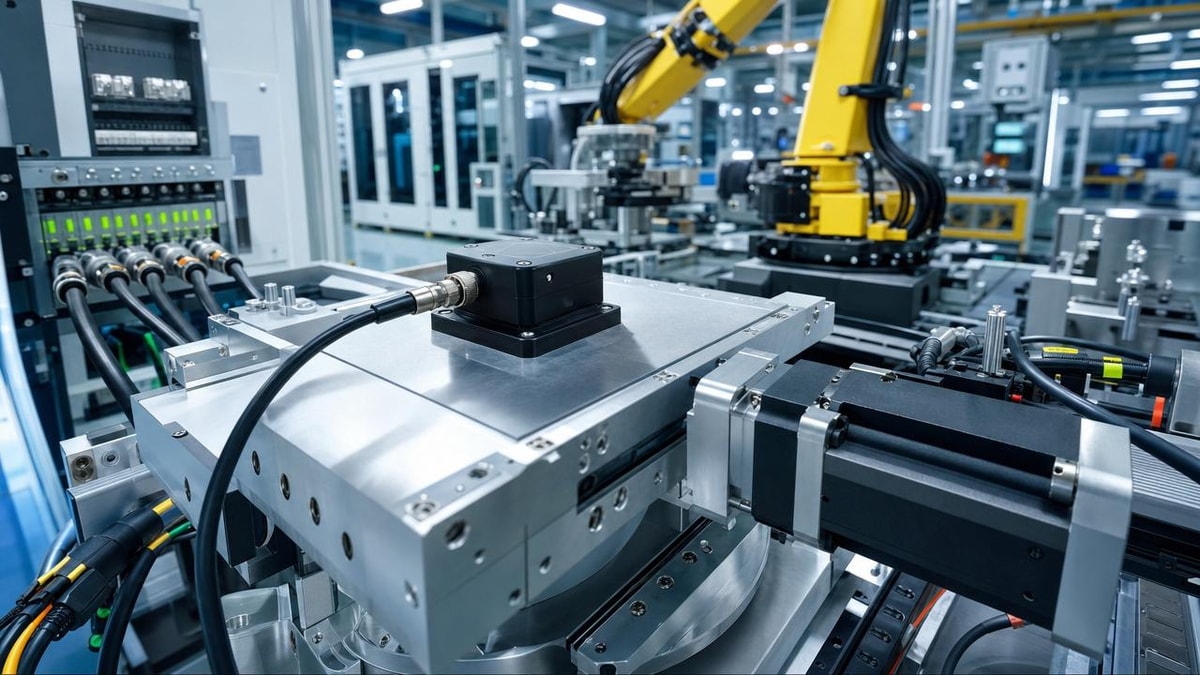
Industrial IoT certification must match the true operating environment, not the catalog ideal. Check for enclosure ratings, contamination limits, vibration tolerance, connector durability, and thermal cycling performance. In sensory-infrastructure applications, even minor thermal stress or particle contamination can distort readings and undermine traceability. If deployment involves cleanrooms, chemical exposure, or high-purity gas areas, confirm material compatibility and contamination-control limits.
4. Data integrity and measurement trust
For quality control teams, a connected device is only as valuable as the trustworthiness of its data. Industrial IoT certification should be evaluated alongside calibration lineage, timestamp reliability, sampling consistency, and error-handling behavior. Ask whether the system flags out-of-range values, missing packets, sensor drift, or synchronization failures. If data is used for batch release, predictive maintenance, or process intervention, unverified measurement integrity becomes a direct quality risk.
5. Cybersecurity baseline and update governance
Many teams treat cybersecurity as separate from Industrial IoT certification, but pre-rollout risk assessment should combine them. Confirm device identity management, access control, encrypted communications, credential storage, logging, patchability, and secure boot behavior where applicable. More importantly, verify who controls updates, how vulnerabilities are disclosed, and whether a firmware update affects certified status. A compliant system at shipment can become a liability if update governance is weak.
A practical review table for quality and safety managers
Use the following decision table to structure internal approval discussions before rollout.
How priorities change by deployment scenario
Industrial IoT certification should not be reviewed in the same way for every site. The checklist must be adjusted to the operational role of the system.
For production quality monitoring
Prioritize sensor accuracy, repeatability, calibration intervals, timestamp integrity, and audit trail quality. If the system supports traceability, lot release, or statistical process control, you should also confirm how data loss, network interruptions, and sensor drift are recorded and escalated.
For safety-critical equipment supervision
Prioritize fail-safe behavior, alarm integrity, power interruption recovery, communication loss handling, and event logging. Safety managers should verify that the Industrial IoT certification package does not imply safety function suitability unless that scope is clearly stated and supported by relevant standards.
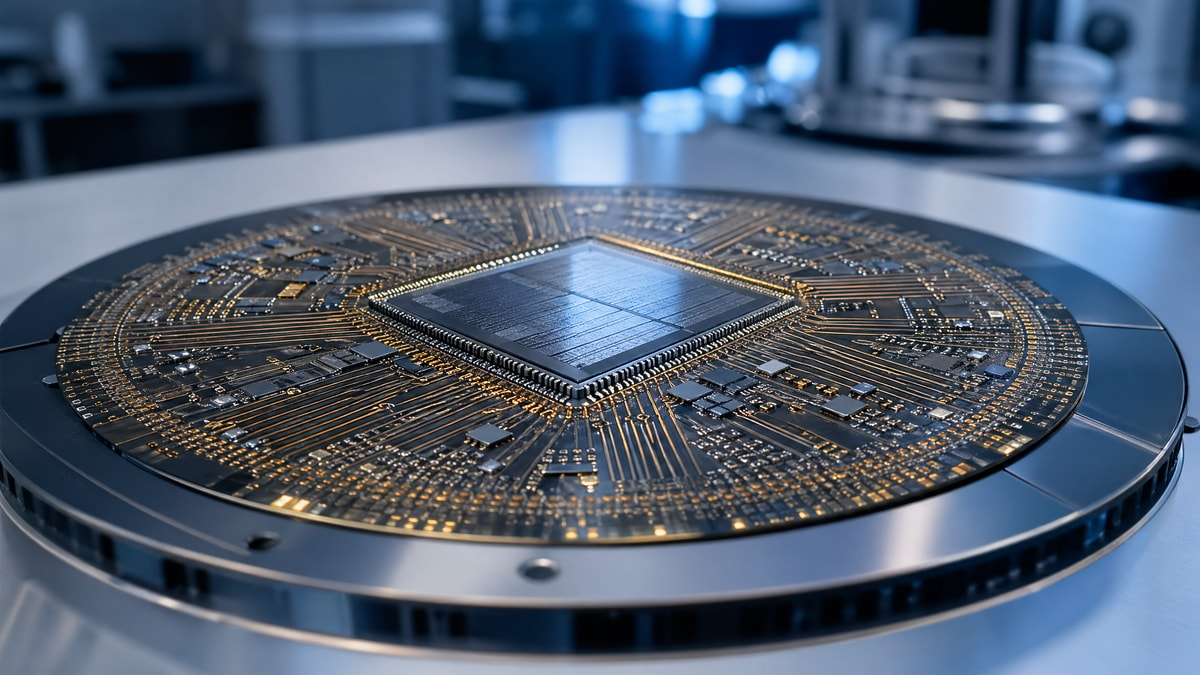
For semiconductor and sensory-infrastructure environments
Prioritize contamination control, thermal stability, EMC resilience, precision measurement behavior, and compatibility with high-purity materials or controlled environments. In these settings, certification quality must support not just uptime, but process precision and material integrity.
Common gaps that teams discover too late
Even experienced plants often miss a few recurring issues when assessing Industrial IoT certification. These should be treated as red-flag review items.
- The device is certified, but the full system integration is not. Gateways, software, cloud connectors, and third-party interfaces may introduce new compliance gaps.
- Certificates are valid geographically, but not for the jurisdiction where the plant operates or exports products.
- Lab conditions do not represent the electromagnetic, thermal, or mechanical stress of the actual production line.
- Calibration was performed initially, but no field recalibration plan exists.
- Firmware updates are pushed after installation without formal impact review on Industrial IoT certification status.
- Responsibility is fragmented between procurement, IT, engineering, and EHS, leaving no single owner for final certification acceptance.
Execution steps before go-live approval
A strong rollout process turns Industrial IoT certification into a controlled approval workflow rather than a passive file collection exercise. The following steps are practical and scalable.
- Create a cross-functional review group with quality, safety, engineering, IT or OT security, and maintenance participation.
- Map each connected asset to its operational role: monitoring only, control influence, safety relevance, or traceability function.
- Request a complete evidence pack from the supplier, including certificates, test reports, calibration records, declarations of conformity, firmware notes, and change control statements.
- Perform a site-condition gap review to compare certified assumptions against real installation stressors.
- Define acceptance criteria for pilot operation, including data stability, alarm accuracy, communication reliability, and maintenance readiness.
- Document recertification triggers such as hardware substitutions, software updates, network architecture changes, or relocation to a different environment.
This process is especially valuable for organizations managing high-value semiconductor, sensor, power electronics, or clean manufacturing assets, where the cost of hidden nonconformity is high.
FAQ: fast answers on Industrial IoT certification before rollout
Is a supplier certificate enough to approve deployment?
No. Industrial IoT certification should be checked against the exact model, site conditions, system interfaces, and intended function. A certificate alone does not guarantee production suitability.
What matters most for quality managers?
Measurement trust. Focus on calibration traceability, drift behavior, timestamp reliability, data completeness, and how exceptions are recorded.
What matters most for safety managers?
Operational failure behavior. Confirm what happens during power loss, network failure, sensor fault, or unauthorized access attempt, and whether alarms remain reliable.
When should recertification be considered?
Whenever there is a meaningful hardware, firmware, environmental, or integration change that may alter tested performance or compliance assumptions.
Final decision guide and next action points
Industrial IoT certification should be treated as a practical readiness checkpoint before system rollout, not as a paperwork milestone. For quality control and safety management teams, the most important question is whether the certified condition truly matches the production reality: the exact device version, the actual operating environment, the required data integrity level, and the plant’s cybersecurity and maintenance practices.
If your organization is preparing to approve a connected system, prioritize these questions in supplier discussions: Which exact configuration was certified? Which standards and laboratories support the claim? What site conditions were assumed? What changes trigger reapproval? How are calibration, firmware control, and vulnerability response managed over time? Those answers will do more to protect uptime, traceability, and compliance than any marketing summary ever will.
If further evaluation is needed, the most useful next step is to align technical parameters, deployment scenario, risk classification, maintenance cycle, budget constraints, and supplier support responsibilities before final rollout approval. That is where Industrial IoT certification becomes a real operational safeguard rather than a formal checkbox.
Get weekly intelligence in your inbox.
No noise. No sponsored content. Pure intelligence.