Industrial IoT Certification Delays and How to Avoid Them
Industrial IoT certification delays can derail launch schedules, inflate compliance costs, and expose critical reliability gaps across connected industrial systems. For project managers and engineering leaders, understanding the root causes—from incomplete testing evidence to misaligned standards and supplier coordination issues—is essential. This article explains why Industrial IoT certification gets delayed and outlines practical steps to keep complex approval processes on track.
What does Industrial IoT certification actually include, and why does it take so long?
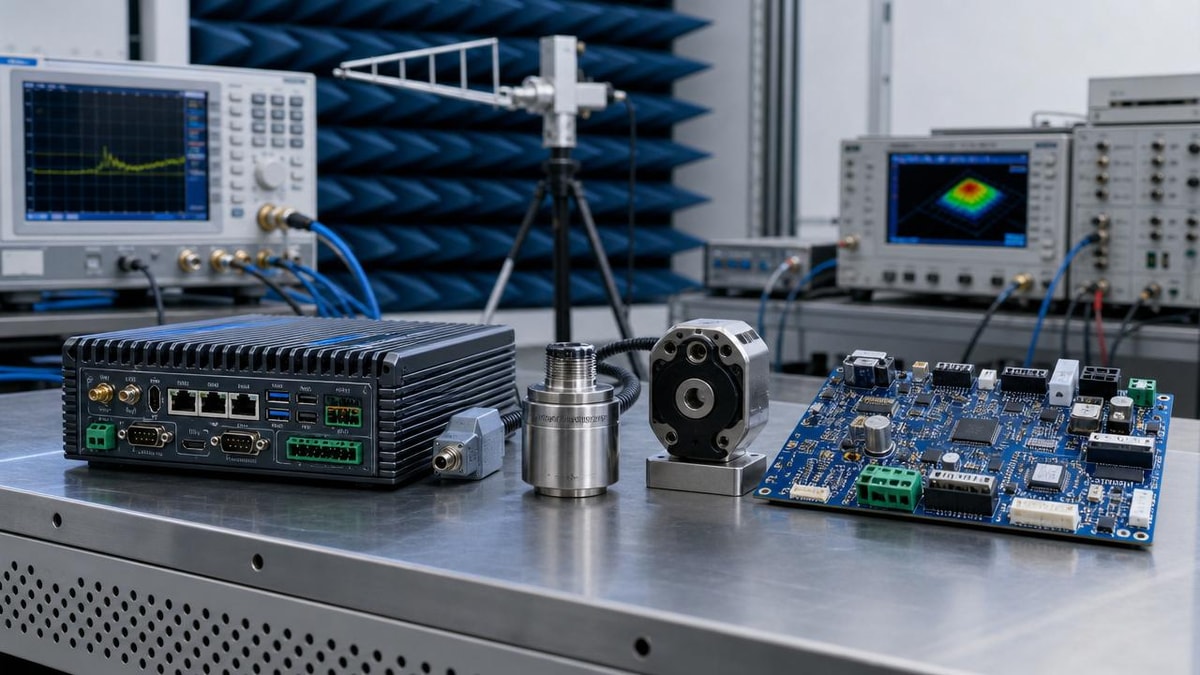
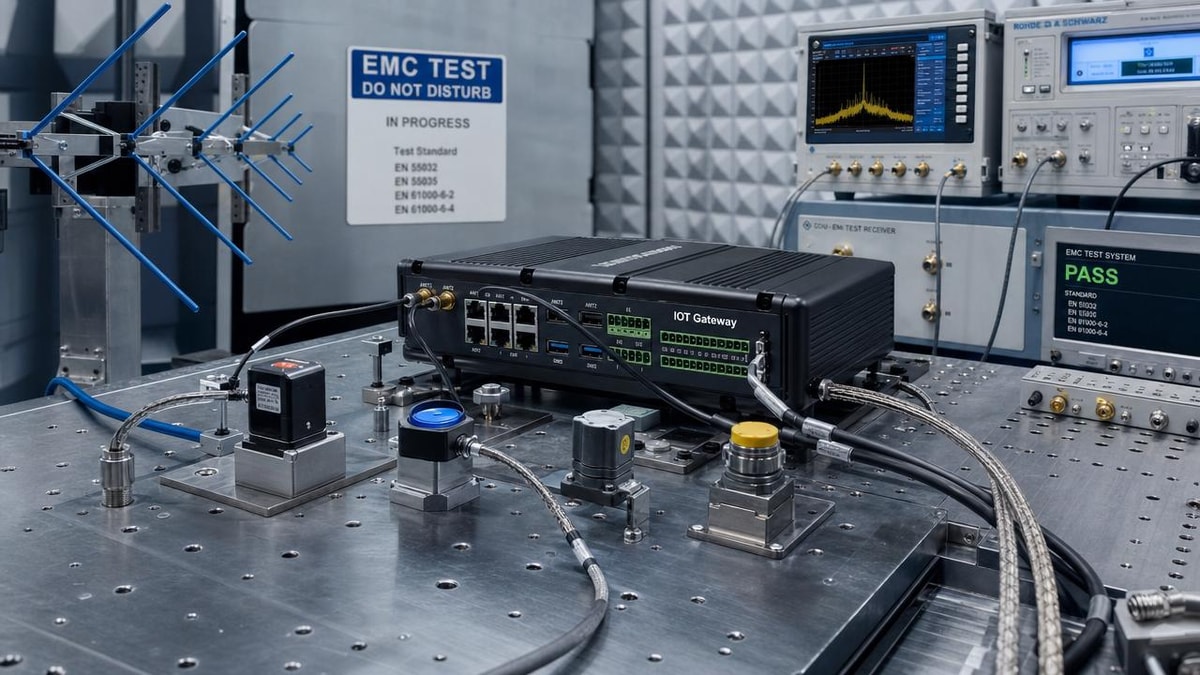
Industrial IoT certification is rarely a single approval step. In most projects, it is a layered process that may involve electrical safety, EMC, radio compliance, cybersecurity, environmental reliability, functional verification, and market-specific documentation. For connected industrial assets, the challenge is that certification often touches both hardware and software, plus the interfaces between sensors, gateways, cloud platforms, power components, and network modules.
That complexity explains why Industrial IoT certification timelines often slip. A device may pass lab tests for one region but fail documentation review in another. A MEMS sensor or communications module may already have sub-certifications, but system-level integration can still create new risks. In sectors where uptime, thermal performance, signal integrity, and data fidelity matter, evidence requirements become even stricter.
For project managers, the biggest mistake is treating certification as a final checkpoint instead of a design stream. In reality, certification readiness should run in parallel with product architecture, supplier qualification, and validation planning. Organizations such as G-SSI emphasize this system-level view because industrial-grade semiconductors, advanced packaging, sensor reliability, and fabrication environment control all affect whether final approval can be achieved without rework.
Why do Industrial IoT certification delays happen so often in real projects?
Most delays do not come from one dramatic failure. They come from small disconnects that accumulate across design, sourcing, testing, and compliance teams. By the time a launch date is fixed, those gaps become schedule blockers.
Common causes include:
- Unclear target markets, which leads to wrong standards or incomplete approval scope.
- Late changes in RF modules, power devices, chip packaging, or firmware versions after pre-compliance tests are complete.
- Insufficient test evidence for temperature cycling, vibration, ingress protection, ESD, surge, or long-duration reliability.
- Supplier data packages that are inconsistent, outdated, or missing traceability.
- Weak coordination between electronics design, embedded software, cybersecurity, and quality documentation teams.
- Underestimating retest cycles after PCB layout changes, enclosure modifications, or thermal redesign.
In Industrial IoT certification, integration is often the real issue. A certified module does not guarantee a certified system. For example, a power semiconductor with strong standalone performance may introduce thermal stress when paired with dense packaging. A high-precision sensor may meet data-sheet claims but drift under enclosure-level heat or vibration. Certification bodies look at actual operating conditions, not just component claims.
Which standards and technical areas create the most confusion for project teams?
Confusion usually starts when teams assume “compliance” means the same thing across all product types. Industrial IoT devices can sit at the intersection of industrial control, communications, energy systems, mobility infrastructure, and data platforms. That means certification pathways vary widely.
The most misunderstood areas are usually:
- Product safety versus system safety: passing one does not automatically satisfy the other.
- Component qualification versus end-product approval: AEC-Q100, SEMI references, or supplier declarations are valuable, but they are not substitutes for end-use verification.
- Lab performance versus field conditions: industrial environments introduce noise, contamination, mechanical stress, and thermal gradients that certification reviewers may expect you to address.
- Cybersecurity versus functional performance: secure firmware updates, authentication, and network hardening can affect timing, interoperability, and documentation scope.
For engineering leaders, the practical lesson is simple: map standards to the exact use case early. If a device is deployed in harsh industrial infrastructure, then environmental controls, reliability evidence, and calibration stability may matter as much as pure connectivity compliance. This is particularly relevant where semiconductor quality, sensor precision, and contamination-sensitive manufacturing processes shape final product consistency.
How can project managers identify delay risks before formal testing begins?
The best time to prevent Industrial IoT certification delays is before the first official submission. Strong teams conduct a certification readiness review during architecture freeze, not after validation is nearly complete.
A useful pre-test review should check five things: target jurisdictions, standards matrix, critical component traceability, evidence completeness, and change-control discipline. If any of those are weak, the schedule is already exposed.
This type of review is especially important when products rely on advanced power devices, high-density packaging, sensitive MEMS components, or contamination-critical materials. In such cases, a small upstream quality variance can become a downstream certification problem.
What are the most effective ways to avoid Industrial IoT certification delays?
Avoiding delay is less about speeding up the lab and more about designing a certifiable product from the start. The following practices create the biggest schedule protection.
1. Build a certification matrix at project kickoff
List target countries, applicable standards, required reports, component dependencies, and owner names. This becomes the control document for the entire project. Without it, Industrial IoT certification usually turns into fragmented email coordination.
2. Run pre-compliance testing before design freeze
Pre-compliance screening for EMC, thermal behavior, power integrity, RF emissions, and enclosure stress is often cheaper than post-failure redesign. It gives teams time to adjust shielding, grounding, stack-up, heat paths, or sensor placement before final tooling is locked.
3. Treat suppliers as part of the certification plan
Ask for declarations, test summaries, material statements, lifecycle status, and traceability data early. If a supplier cannot support reliability evidence or controlled change notification, the risk is not only procurement-related; it directly affects Industrial IoT certification timing.
4. Align cybersecurity and hardware teams sooner
Security features such as encrypted boot, remote updates, network isolation, and credential handling can change system behavior and test documentation. If security is added late, teams often face integration instability and paperwork gaps.
5. Lock down change control during validation
A disciplined engineering change process is one of the simplest ways to avoid avoidable retests. Every firmware revision, PCB change, package substitution, or sensor recalibration should be reviewed for compliance impact before release.
What mistakes do teams make when they assume certification is “almost done”?
Many teams believe they are close to completion because the prototype works well, the main lab test passed, or a major component is already approved. But Industrial IoT certification can still stall at the final stage for reasons that feel administrative yet have real technical consequences.
Typical late-stage mistakes include incomplete technical files, inconsistent product labeling, unsupported software version histories, missing calibration records, and unresolved differences between pilot-build units and final production units. Another common issue is assuming the test sample represents mass production, even though actual assembly processes, environmental controls, or material lots are different.
This is why high-reliability organizations focus on traceability and manufacturing discipline. If packaging quality, gas purity, contamination control, or sensor calibration stability vary between batches, certification confidence can weaken. Reviewers and customers both want evidence that compliance is repeatable, not accidental.
How should project managers plan schedule, budget, and stakeholder communication around certification?
The safest planning model is to treat Industrial IoT certification as a workstream with technical, commercial, and supply-chain milestones. Build buffer for pre-testing, documentation consolidation, retest windows, and reviewer response cycles. If the product includes custom sensing, power conversion, or advanced semiconductor integration, add more contingency, not less.
Budget planning should include more than lab fees. It should also cover engineering rework, consultant support if needed, sample builds, fixture updates, travel, supplier follow-up, and opportunity cost from delayed market entry. For many industrial products, the real cost of certification delay is not the test invoice; it is missing a deployment window, tender, or customer acceptance milestone.
Communication is equally critical. Senior stakeholders need a simple view of readiness: what is approved, what is pending, what could trigger retest, and which supplier inputs are still open. A weekly certification dashboard with red-flag items is often more valuable than a long technical memo.
When should a company bring in outside technical support or benchmarking guidance?
External support becomes valuable when the product combines multiple difficult variables: industrial-grade sensors, high-voltage or high-efficiency power electronics, advanced packaging, strict contamination requirements, or cross-border compliance targets. In these situations, benchmarking against recognized technical frameworks can shorten decision time and reduce blind spots.
A technical hub such as G-SSI can be useful because certification outcomes are often shaped by upstream engineering quality, not just final testing. If you need to compare SiC or GaN power behavior, packaging reliability, sensor stability, chemical purity impact, or environmental control capability against standards such as SEMI, AEC-Q100, or ISO/IEC 17025, independent benchmarking helps teams make stronger design and sourcing choices earlier.
For project managers, the goal is not to outsource ownership. It is to validate assumptions before they become delays. The earlier you confirm risk areas, the more leverage you keep over budget, timeline, and launch confidence.
What should you confirm first before moving forward with an Industrial IoT certification plan?
Before committing to final schedules, confirm five points: the exact market access scope, the standards that truly apply, the frozen configuration of key hardware and firmware, the completeness of supplier compliance evidence, and the expected operating environment in the field. These five answers usually determine whether Industrial IoT certification proceeds smoothly or becomes a costly sequence of retests and exceptions.
If you need to confirm a practical path forward, start the conversation around these questions: Which standards and regions matter most first? Which semiconductors, sensors, and modules are still subject to change? What evidence already exists for reliability, thermal performance, and traceability? Where are the largest risks in packaging, environmental control, or supply consistency? And what timeline buffer is realistic for pre-compliance, formal testing, and corrective action? Clarifying those points early is the fastest way to reduce Industrial IoT certification delays and keep industrial programs launch-ready.
Get weekly intelligence in your inbox.
No noise. No sponsored content. Pure intelligence.